Trinoo Software Download
What is DDoS-Trinoo? DDoS-Trinoo is considered to be a virus, a type of malware that is designed to create havoc in your computer.
A DDoS-Trinoo infection can be as harmless as showing annoying messages on your screen, or as vicious as disabling your computer altogether. Regardless of the virus' behavior, the primary objective of computer hackers who program viruses such as like DDoS-Trinoo is to delete, destroy, or steal data. What are Viruses? Computer viruses such as DDoS-Trinoo are software programs that infect your computer to disrupt its normal functioning without your knowledge. Typically, a virus gains entry on your computer as an isolated piece of executable code or by through bundling / piggybacking with other software programs.
Once a virus such as DDoS-Trinoo gains entry into your computer, the symptoms of infection can vary depending on the type of virus. Some viruses can keep adding shortcuts of other programs on your desktop, while others can start running unwanted programs, also referred as “PUP” (Potentially Unwanted Programs) to intentionally slow down your computer. There are also more harmful viruses that present the infamous “blue screen of death”, a critical system error that forces you to keep restarting your computer. Viruses like DDoS-Trinoo can even delete your important files and folders.
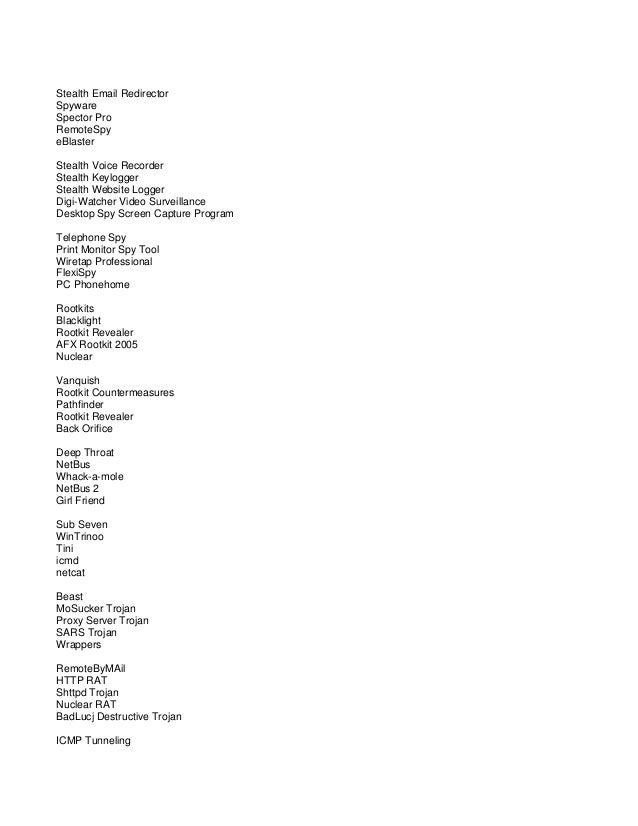
Trinoo becomes a Trojan. The denial-of-service tool known as Trinoo has been ported to Windows 9x/2000, announced several security and antivirus companies this week.
Finally, more severe strains of viruses are able to damage the operating system by modifying system level files and Windows Registry - with the sole intention to make your computer unusable. How did DDoS-Trinoo get on my Computer? DDoS-Trinoo can gain entry onto your computer in several ways. Removal Solution: Use an Anti-Malware Program We recommend using ClamWin (free download), a highly effective and widely used malware removal program to clean your computer of DDoS-Trinoo. In addition to DDoS-Trinoo, this program can detect and remove the latest variants of other malware. ClamWin has an intuitive user interface that is easy to use. To get rid of DDoS-Trinoo, the first step is to install it, scan your computer, and remove the threat.
To remove DDoS-Trinoo from your computer using ClamWin, you need to perform the following steps. Conclusion Viruses such as DDoS-Trinoo can cause immense disruption to your computer activities. The best method for avoiding infection is prevention; avoid downloading and installing programs from untrusted sources or opening executable mail attachments. Following these simple preventative measures will ensure that your computer remains free of infections like DDoS-Trinoo, and provide you with interruption-free enjoyment of your computer. Are You Still Experiencing DDoS-Trinoo Issues? Please reach out to us anytime on social media for more help.
Solvusoft: Microsoft Gold Certified Company Recognized for best-in-class capabilities as an ISV (Independent Software Vendor) Solvusoft is recognized by Microsoft as a leading Independent Software Vendor, achieving the highest level of completence and excellence in software development. Solvusoft's close relationship with Microsoft as a Gold Certified Partner enables us to provide best-in-class software solutions that are optimized for performance on Windows operating systems. How is the Gold Competency Level Attained? To achieve a Gold competency level, Solvusoft goes through extensive independent analysis that looks for, amongst other qualities, a high level of software expertise, a successful customer service track record, and top-tier customer value. As a Gold Certified Independent Software Vendor (ISV), Solvusoft is able to provide the highest level of customer satisfaction through delivering top-level software and service solutions, which have been subject to a rigourous and continually-audited approval process by Microsoft.
Tribe Flood Network, like trinoo, uses a master program to communicate with attack agents located across multiple networks. TFN launches coordinated Denial of Service Attacks that are especially difficult to counter as it can generate multiple types of attacks and it can generate packets with spoofed source IP addresses. Some of the attacks that can be launched by TFN include UDP flood, TCP SYN flood, ICMP echo request flood, and ICMP directed broadcast. The basic characteristics of and suggested defense strategies against the TFN DDoS attack follow. To initiate TFN, the attacker accesses the master program and sends it the IP address of one or more targets. The master program proceeds to communicate with all of the agent programs, instructing them to initiate the attack.
Communications between TFN master programs and agent programs use ICMP echo reply packets, where the actual instruction to be carried out is embedded in the 16-bit ID field in binary format. The use of ICMP (Internet Control Message Protocol) makes packet protocol filtering possible.
TFN agents can be defeated by configuring your router or intrusion detection system to disallow all ICMP echo and echo reply packets onto your network. However, this will break all internet programs (such as 'ping') that utilize these functions. The TFN master program reads a list of IP addresses containing the locations of the agents programs. This list of addresses may be encrypted, using 'Blowfish' encryption. If it is not encrypted, then the agents can be identified from the list.
The TFN agent programs have been found on systems with the filename td and the master programs with the name tfn. They can be positively identified by running the UNIX strings command. TFN agents do not check where the ICMP echo reply packets come from.
Therefore, it is possible to forge ICMP packets to flush out these processes. TFN is made up of client and daemon programs, which implement a distributed network denial of service tool capable of waging ICMP flood, SYN flood, UDP flood, and Smurf style attacks, as well as providing an 'on demand' root shell bound to a TCP port. The TFN network is made up of a tribe client program ('tribe.c') and the tribe daemon ('td.c'). The attacker(s) control one or more clients, each of which can control many daemons. The daemons are all instructed to coordinate a packet based attack against one or more victim systems by the client. Remote control of a TFN network is accomplished via command line execution of the client program, which can be accomplished using any of a number of connection methods (e.g., remote shell bound to a TCP port, UDP based client/server remote shells, ICMP based client/server shells such as LOKI, SSH terminal sessions, or normal 'telnet' TCP terminal sessions.) No password is required to run the client, although it is necessary to have the list of daemons at hand in an 'iplist' file. Communication from the TFN client to daemons is accomplished via ICMPECHOREPLY packets.
There is no TCP or UDP based communication between the client and daemons at all. While the client is not password protected, per se, each 'command' to the daemons is sent in the form of a 16 bit binary number in the id field of an ICMPECHOREPLY packet. (The sequence number is a constant 0x0000, which would make it look like the response to the initial packet sent out by the 'ping' command.) The values of these numbers, as well as macros that change the name of the running process as seen by PS (1) are defined by the file 'config.h'.
As with trinoo, the method used to install the client/daemon will be the same as installing any program on a UNIX system, with all the standard options for concealing the programs and files. Both the client and the daemon must be run as root, as they both open an AFINET socket in SOCKRAW mode.
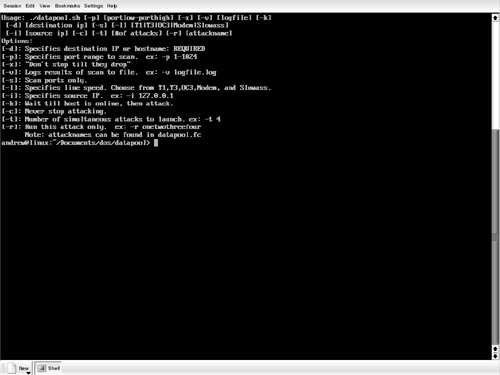
The client program requires the iplist be available. Recent installations of TFN daemons have included strings that indicate the author is (or has) added Blowfish encryption of the iplist file. This will make the task of determining the daemons much harder. Detecting trinoo/TFN related attacks: Several conventional attacks are known to be related to trinoo/TFN compromises. Machines that are compromised using the following list of attacks should be checked for trinoo/TFN daemons: -rpc.ttdbserver -amd -rpc.cmsd -rpc.mountd -rpc.statd. Running the server #td Running the client #tn -h 23.4.56.4 -c8 -i 56.3.4.5 This command starts an attack from 23.4.56.4 to the victim's computer 56.3.4.5 The TFN2K distributed denial of service system consists of client/server architecture. The Client: The client is used to connect to master servers, which can then perform specified attacks against one or more victim machines.
Commands are sent from the client to the master server within the data fields of ICMP, UDP, and TCP packets. The data fields are encrypted using the CAST algorithm and base64 encoded. The client can specify the use of random TCP/UDP port numbers and source IP addresses. The system can also send out 'decoy' packets to non-target machines.
These factors make TFN2K more difficult to detect than the original TFN program. The Master Server: The master server parses all UDP, TCP, and ICMP echo reply packets for encrypted commands. The master server does not use a default password when it is selected by the user at compile time. Attack Methods The Attack: The TFN2K client can be used to send various commands to the master for execution, including commands to flood a target machine or set of target machines within a specified address range. The client can send commands using UDP, SYN, ICMP echo, and ICMP broadcast packets. These flood attacks cause the target machine to slow down because of the processing required to handle the incoming packets, leaving little or no network bandwidth. TFN2K can also be used to execute remote commands on the master server and bind shells to a specified TCP port.
TFN2K runs on Linux, Solaris, and Windows platforms. Hacking Tool: Stacheldraht. Stacheldraht consists of three parts: the master server, client, and agent programs. The Client: The client is used to connect to the master server on port 16660 or port 60001. Packet contents are blowfish encrypted using the default password 'sicken', which can be changed by editing the Stacheldraht source code.
After entering the password, an attacker can use the client to manage Stacheldraht agents, IP addresses of attack victims, lists of master servers, and to perform DoS attacks against specified machines. The Master Server: The master server handles all communication between client and agent programs.
It listens for connections from the client on port 16660 or 60001. When a client connects to the master, the master waits for the password before returning information about agent programs to the client and processing commands from the client.
Software Download Windows 10
The Agent: The agent listens for commands from master servers on port 65000. In addition to this port, master server/agent communications are also managed using ICMP echo reply packets. These packets are transmitted and replied to periodically. They contain specific values in the ID field (such as 666, 667, 668, and 669) and corresponding plaintext strings in the data fields (including 'skillz', 'ficken', and 'spoofworks'). The ICMP packets act as a 'heartbeat' between agent and master server, and to determine source IP spoofing capabilities of the master server.
The agent identifies master servers using an internal address list, and an external encrypted file containing master server IP addresses. Agents can be directed to 'upgrade' themselves by downloading a fresh copy of the agent program and deleting the old image as well as accepting commands to execute flood attacks against target machines.
The Attack: Like TFN/TFN2K, Stacheldraht can be used to perform ICMP, SYN, and UDP flood attacks. The attacks can run for a specified duration, and SYN floods can be directed to a set of specified ports. These flood attacks cause the target machine to slow down because of the processing required to handle the incoming packets, leaving little or no network bandwidth.
Stacheldraht (German for 'barbed wire') combines features of the 'trinoo' distributed denial of service tool, with those of the original TFN, and adds encryption of communication between the attacker and stacheldraht masters and automated update of the agents. One of the weaknesses of TFN was that the attacker's connection to the master(s) that control the network was in clear-text form, and was subject to standard TCP attacks (session hijacking, RST sniping, etc.) Stacheldraht deals with this by adding an encrypting 'telnet alike' (stacheldraht term) client. The attacker(s) control one or more handlers using encrypting clients. Each handler can control many agents (up to 1000 agents).
The agents are all instructed to coordinate a packet-based attack against one or more victim systems by the handler. Unlike trinoo, which uses UDP for communication between handlers and agents, or the original Tribe Flood Network, which uses ICMP for communication between the handler and agents, stacheldraht uses TCP and ICMP. Client to handler(s): 16660/tcp and Handler to/from agent(s): 65000/tcp, ICMPECHOREPLY. Remote control of a stacheldraht network is accomplished using a simple client that uses symmetric key encryption for communication between itself and the handler. After connecting to the handler using the client program, the attacker is prompted for a password. This password (default 'sicken') is a standard crypt encrypted password, which is then Blowfish encrypted using the passphrase 'authentication' before being sent over the network to the handler.
 In Grand Theft Auto V demo takes on three completely different characters: Michael – a former bank robber from the east coast, under the protection of the witness protection program, Trevor – military pilot in the resting state, suffering from mental disorders and Franklin – the boy from the ghetto, recovering cars from insolvent customers Armenian local dealer. After long expectations have decided to release a completely free GTA 5 demo to download. GTA 5 Demo Download For PC – GTA 5 Demo Download Game GTA 5 demo download PC is the first time in history, in which the company producing the game Grand Theft Auto has released a demo version of the game and it happened, because for a long time been slow to release the game on PC.
In Grand Theft Auto V demo takes on three completely different characters: Michael – a former bank robber from the east coast, under the protection of the witness protection program, Trevor – military pilot in the resting state, suffering from mental disorders and Franklin – the boy from the ghetto, recovering cars from insolvent customers Armenian local dealer. After long expectations have decided to release a completely free GTA 5 demo to download. GTA 5 Demo Download For PC – GTA 5 Demo Download Game GTA 5 demo download PC is the first time in history, in which the company producing the game Grand Theft Auto has released a demo version of the game and it happened, because for a long time been slow to release the game on PC.
Software Download Sites
One feature of stacheldraht not shared by trinoo or TFN is the ability to upgrade the agents on demand. This feature employs the Berkeley 'rcp' command (514/tcp), using a stolen account at some site as a cache. On demand, all agents are instructed to delete the current program image, go out and get a new copy (either Linux- or Solaris-specific binary) from a site/account using 'rcp', start running this new image with 'nohup', and then exit. When each agent starts up, it attempts to read a master server configuration file to learn which handler(s) may control it. This file is a list of IP addresses, encrypted using Blowfish, with a passphrase of 'randomsucks'. Failing to find a configuration file, there are one or more default handler IP addresses compiled into the program.
Software Download
Once the agent has determined a list of potential handlers, it then starts at the beginning of the list of handlers and sends an ICMPECHOREPLY packet with an ID field containing the value 666 and data field containing the string 'skillz'. If the master gets this packet, it sends back an ICMPECHOREPLY packet with an ID field containing the value 667 and data field containing the string 'ficken'. In addition to finding an active handler, the agent performs a test to see if the network on which the agent is running allows packets to exit with forged source addresses.
It does this by sending out an ICMP ECHO packet with a forged IP address of '3.3.3.3', an ID of 666, and the IP address of the agent system (obtained by getting the hostname, then resolving this to an IP address) in the data field of the ICMP packet. If the master receives this packet, it replies to the IP address embedded in the packet with an ICMPECHOREPLY packet containing an ID of 1000 and the word 'spoofworks' in the data field. If the agent receives this packet, it sets a spooflevel of zero (can spoof all 32 bits of IP address). If it times out before receiving a spoof reply packet, it sets a spooflevel of 3 (can only spoof the final octet).Regards, Amarjit Singh.